
ScienceEtonnante 3 years ago
Je vous présente une technique redoutable pour déchiffrer les messages codés, technique malgré tout très simple à programmer ...

astuces informatiques blaise 2 years ago

AFP 10 years ago
Les URL, adresses web, ont envahi la toile. Mais comment fonctionnent-elles ? Explications. VIDEOGRAPHIE.

Aryan 4 years ago
So I know a lot of people have gone through a website that blocks content until you pay for their premium service or make an ...
WayToLearnX A year ago
Outil: https://tools.waytolearnx.com/fr/base64-decoder Un décodeur Base64 est un outil en ligne qui inverse le processus ...

Dion Training 4 years ago
My 14 year old son thinks he is hilarious... I just noticed he changed his discord status to this: ...

WayToLearnX A year ago
Outil: https://tools.waytolearnx.com/fr/html-entity-converter Le convertisseur d'entités HTML est un outil qui vous aide à convertir ...

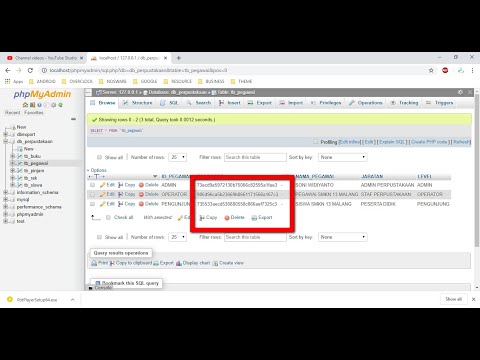
Emwald85 : Developpement Web & Multimedia 5 years ago
+150 Logiciels GRATUITS & Autres : https://contenus.site Je te Montre Dans Cette video TUTO : 👌 Comment Afficher ou Faire ...

Pass2hack 11 years ago
Salut dans cette video je vous montrer comment décrypter un mot de passe ou texte crypter en différentes encryptions Le site qui ...

sec right 3 years ago
One of the first things I remember doing as a kid was writing secret messages to friends using invisible ink. In digital world you can ...

La séduction selon James D. 4 years ago
Décoder les SMS d'une femme ! Comment décrypter les SMS d'une femme, comment analyser les SMS d'une femme? Souvent ...

InfoTuto 7 years ago
La plupart des navigateurs web modernes disposent d'outils mis à disposition des développeurs pour bidouiller un certain ...

Théorisons 8 years ago
Pouvoir hacker n'importe quel mot de passe est le rêve de chacun. Pourtant il existe bien des méthodes pour réussir. La méthode ...

Th3techi3s 12 years ago
Thanks for watching, i hope you enjoyed the video tutorial. Notepad++: ...

local guy 9 years ago
How to Read WhatsApp Database Crypt5 Crypt7 Crypt8.how to read someone's whatsapp messages using WhatsApp database ...

TitanTech 2 years ago
Create a Spiderman using python coding. In this video we learn about how to make a Spiderman using python coding/python ...
WareData 5 years ago
Tutorial How to Decrypt or See MD5 Password.

Numelion IT [Tutoriels] 5 years ago
Vous souhaitez crypter un fichier rapidement ? Pardonnez-moi cet abus de langage, car on ne dit pas crypter un fichier mais ...

Gauging Gadgets 5 years ago
How to hide a file inside of an image? In this tutorial, I show you how to hide a file inside of an image file. This is a great way to ...

VERY MATH TRIP - Manu Houdart 3 years ago
À la fin des années '60, un tueur sème la panique dans toute la Californie. Il revendique ses crimes odieux en adressant des ...

UniqueTutorials 2 years ago
This video tutorial is all about How to Encrypt or Decrypt any File for free in any Windows Computer. #encryt #decrypt ...

CodeBytes101 A year ago
shorts #viral #viralshorts #programming #python #modern #gui #tkintertutorial #tkinter #cryptography.

En 1 minute 2 years ago
Comment afficher le code source html css javascript d'une page internet web à partir du navigateur internet google chrome pour ...

Her-Best Informatique 2 years ago
hacking #hack #pirater_un_reseau_wifi #trouver_le_mot_de_passe_d_un_wifi #hacker_un_wifi_securise #pirater_wifi ...

Tinkernut 13 years ago
Description: If you're into making secret messages, this episode will show you how you can embed text and images into audio ...

Devslopes 2 years ago

WEB CIFAR 4 years ago
Today we are going to build a binary decoder with vanilla JavaScript. Where you can decode your binary code to plain text and ...

The Technology Firm 7 years ago
Wireshark does a great job Identifying, Decoding, Dissecting and presenting packets and their associated packets. Every so often ...

Tech Raj 6 years ago
In this video, we'll see how hackers really crack passwords. How to setup 2FA on social media: ...

Virbox 2 years ago
Seems like I should use Python for my distributed computing project... Context: ...

Chris Greer 4 years ago
In this tutorial, we are going to capture the client side session keys by setting an environment variable in Windows, then feed them ...

selfhelpsonya A year ago

Fast Programming 3 years ago
Normal People VS Programmers #coding #python #programming #easy #funny #short.

WhiteBatCodes 3 years ago
using Java Ciphers to encrypt and decrypt Strings. Code can be found here: ...
Option Alternative 4 years ago
COMMENT DECRYPTER LES MESSAGES DE VOTRE INCONSCIENT POUR VOTRE ANALYSE PSYCHOLOGIQUE?

PiParts A year ago
joinus calculator casio cheating exams.

Brian Veitch 11 years ago
This video explains how to use my online shift cipher tool. http://brianveitch.com/maze-runner/caesar/index.html ...

MeOnTech 9 years ago
Please visit my Amazon A store for some great Radio Products. http://astore.amazon.com/af5dn-20 Please visit my web page ...

Moogs 2 years ago
UPDATE 6/6/23 ***** THIS STILL WORKS How to set a default HDMI input when you turn on your display. This is good for PC or ...

Alok Speaks 2 years ago
Editing credit ~ Midhun my friend LOVELY PROFESSIONAL UNIVERSITY Hi everyone welcome back to my channel . So ,yes on ...

PromisKeeper 7 years ago
Super easy way to save a PDF and lose the security restrictions for editing. Any web browser should work. Bing, Edge, Internet ...

Géomatique Pour Débutants 3 years ago
convertir un fichier csv en fichier Excel #excel #exceltutorial.

Sonoftheprophet 3 years ago
Son of the prophet danced exactly like Dr Paul Eneche and Bishop David Oyedepo. #sonoftheprophet #hilarious #stayconnected ...

howto 7 years ago
Excel file use ASCII encoding format by default. But, when there are special characters in file. you have to make sure to save file ...

sansCARi sumit A year ago

Max's Tech 7 years ago
Thanks for watching everyone! Have any questions? Leave a comment below! ASCII Table ...

John Hammond A year ago
https://j-h.io/passbolt || Use a password manager to keep all your credentials secure -- my code JOHN-HAMMOND will save 20% ...

Hafnium - Sécurité informatique 4 years ago
Télécharger le guide complet pour débuter dans la cybersécuirté ...

AurlomTV 8 years ago
Méthodes, techniques, astuces et entraînement pour le Tage Mage, le Score IAE Message, le Tage 2 et d'autres tests ...
